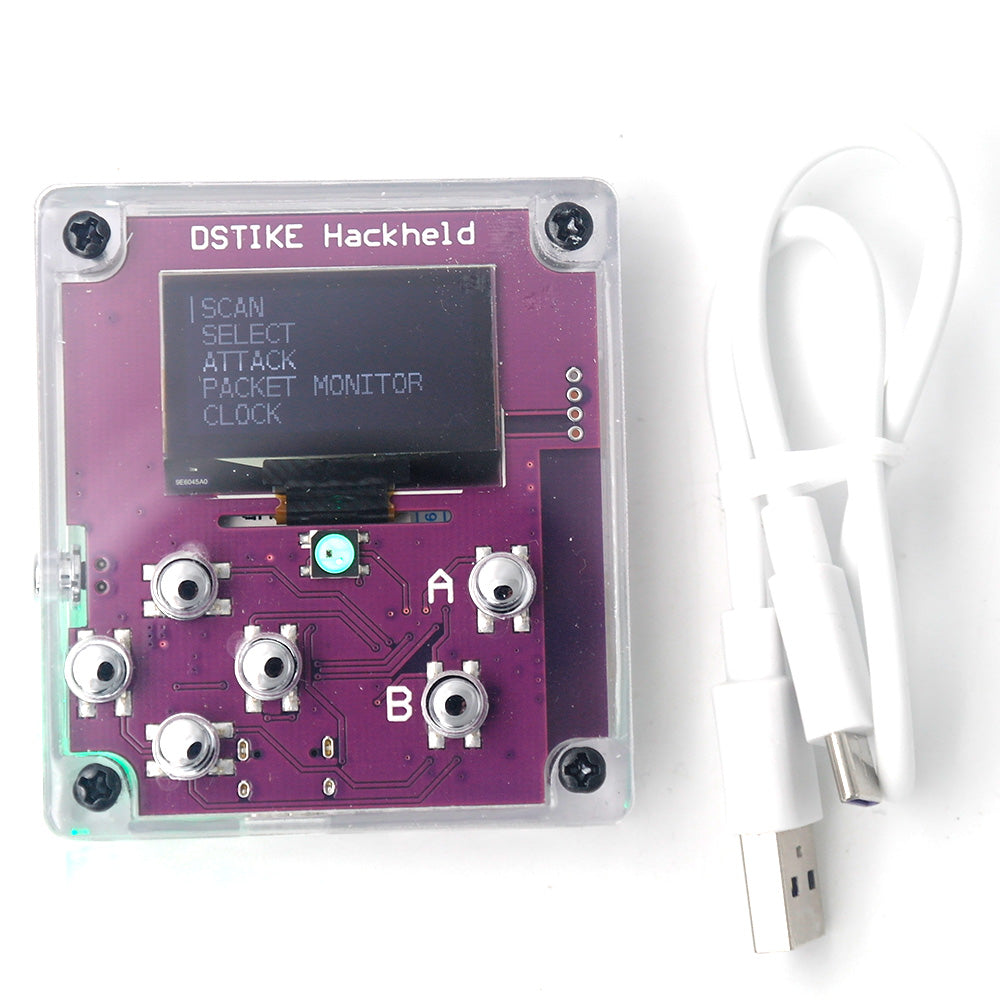
DSTIKE HACKHELD | 2.4G Wi-Fi Attack Security Testing Geek Device
Reliable shipping
Flexible returns
What is it?
Hackheld is a open source hackable handheld for DIY. It comes installed with the latest ESP8266 Deauther software. With this software, you can perform different attacks to test WiFi networks.
Please note that the ESP8266 does only support 2.4GHz.
You can also use it to develop your own software. It is simple to use, just like any other ESP8266 development board.
Function
- Deauther Attack: Disconnect 2.4G WiFi
- Deauther Beacon: Create fake networks
- Deauther Probe:Confuse wifi trackers
- Packet Monitor:Display wifi traffic
Why did you make it?
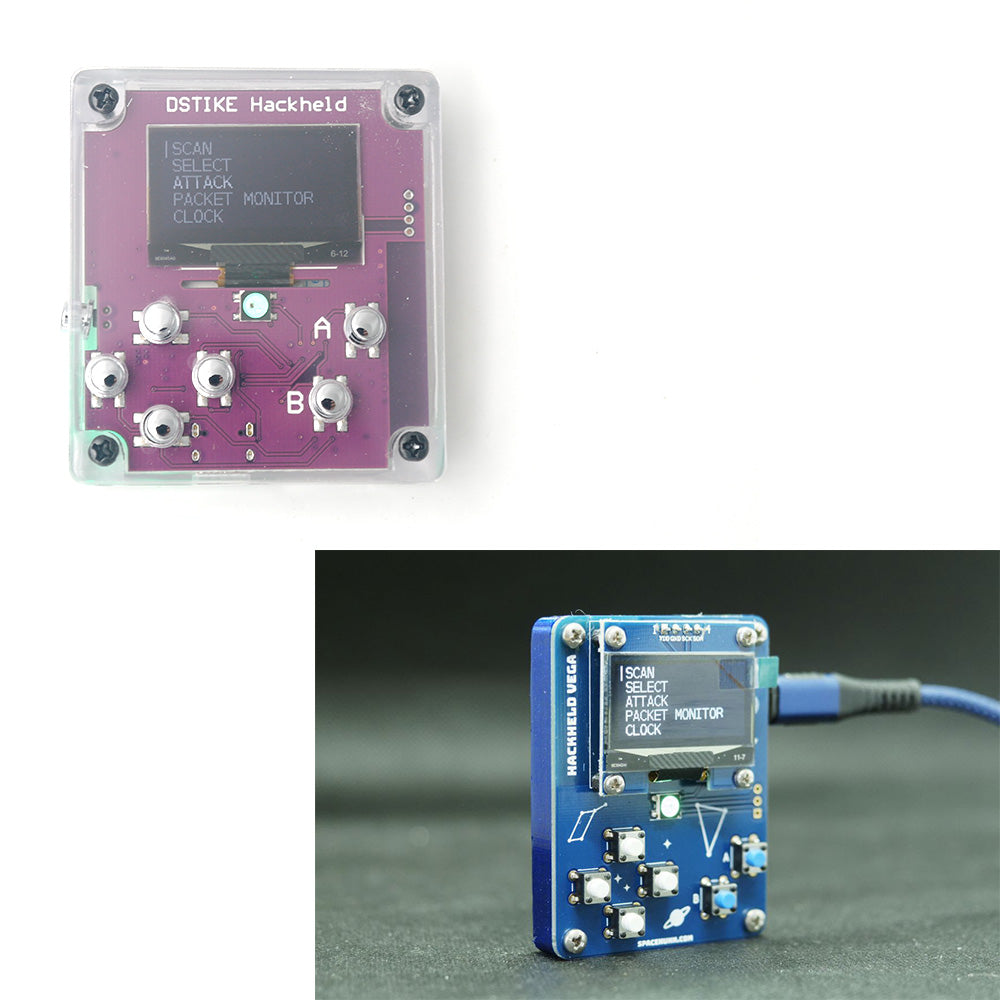
I designed this development board especially for Spacehuhn's great project:Hackheld. It has been authorized by him and is officially supported.
Thanks to every customer that leaves feedback! I will keep improving this board.
What makes it special?
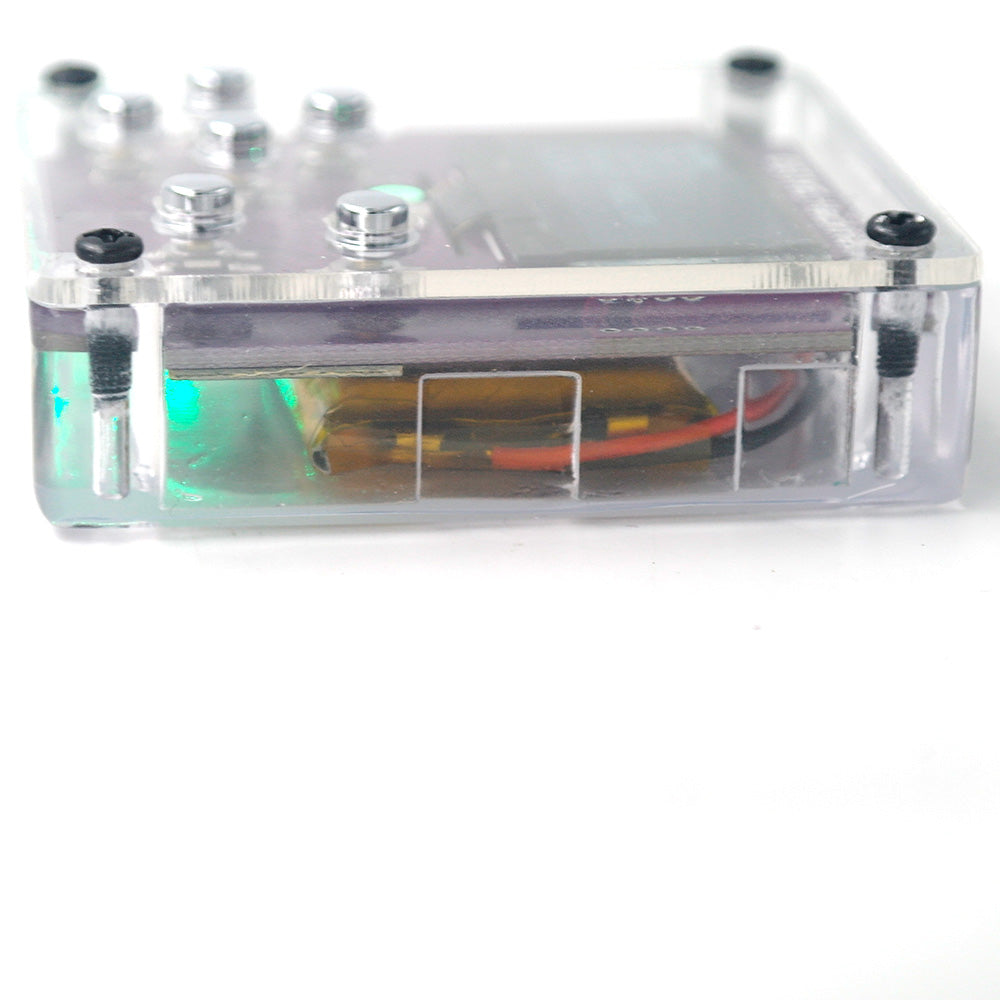
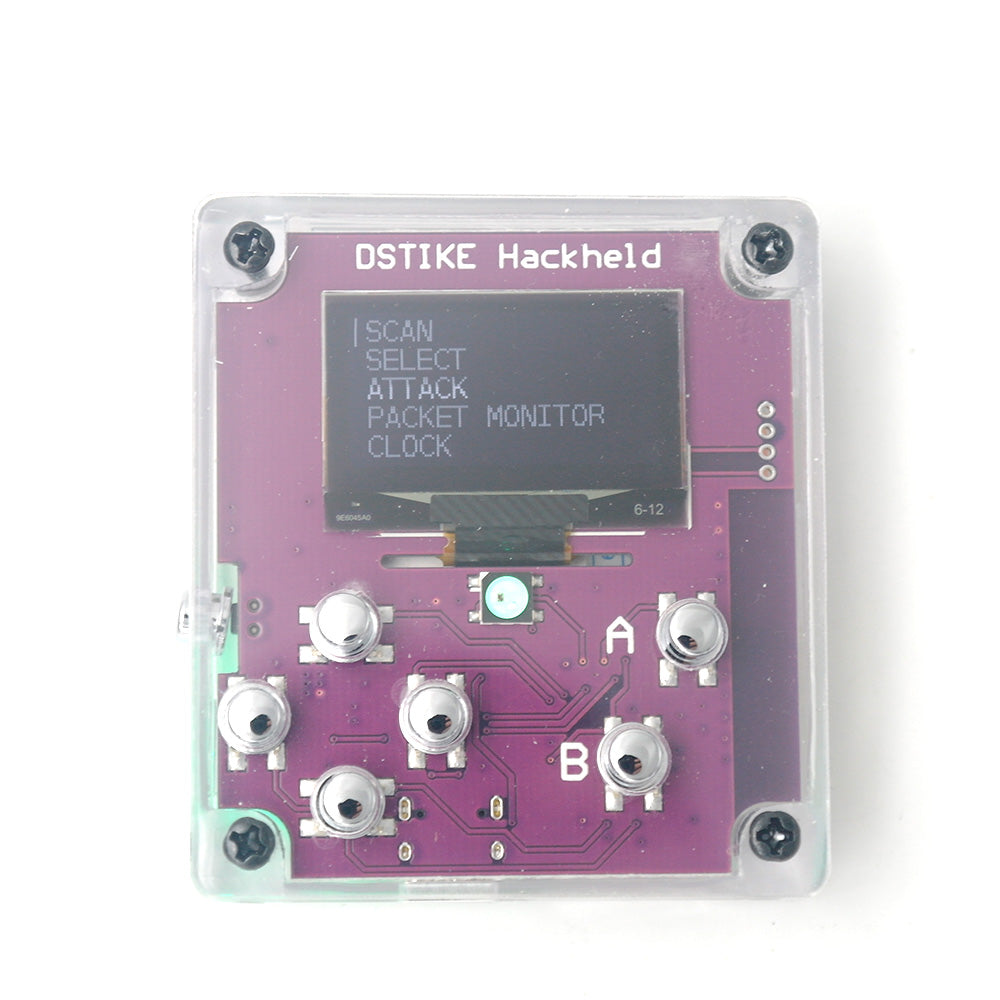
- Arcylic cover and 3D print transparent case
- Indicate charging LED (25%,50%,75%,100%)
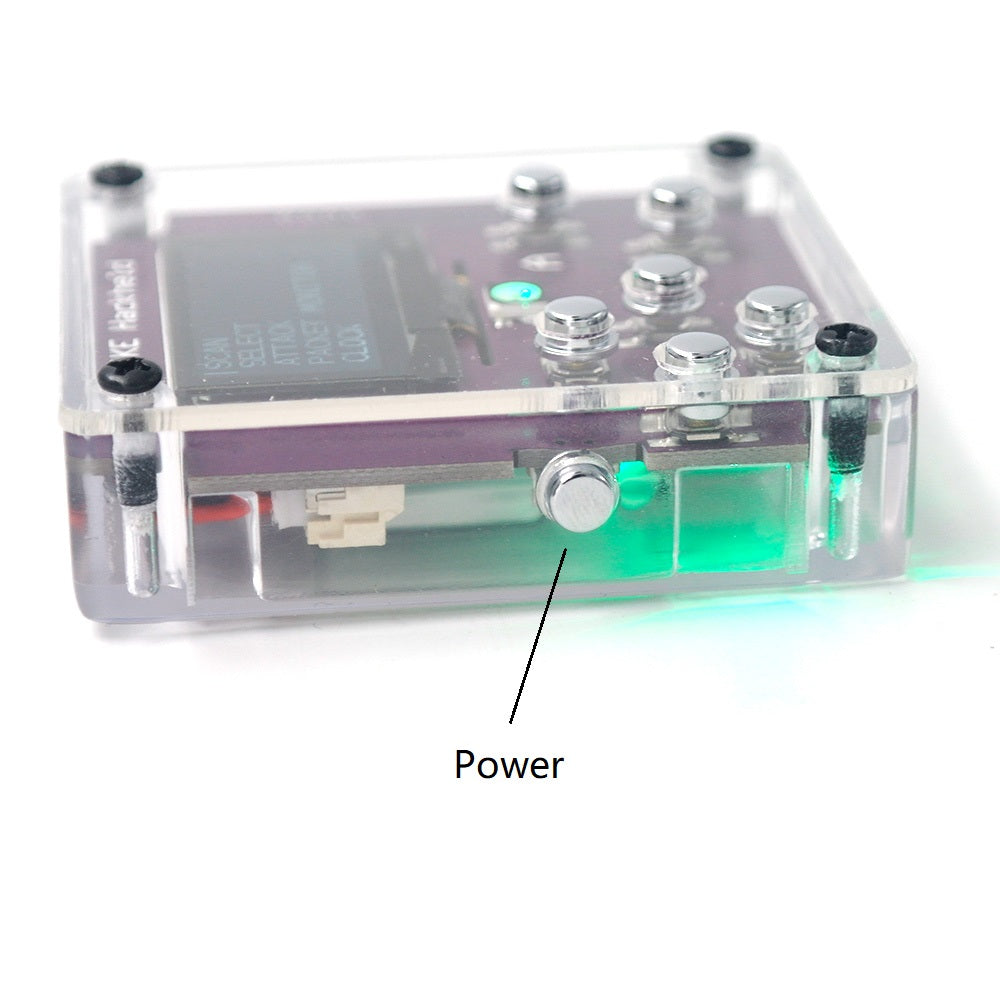
- Power Switch (Click to turn on, double click to turn off,long click to open flashlight)
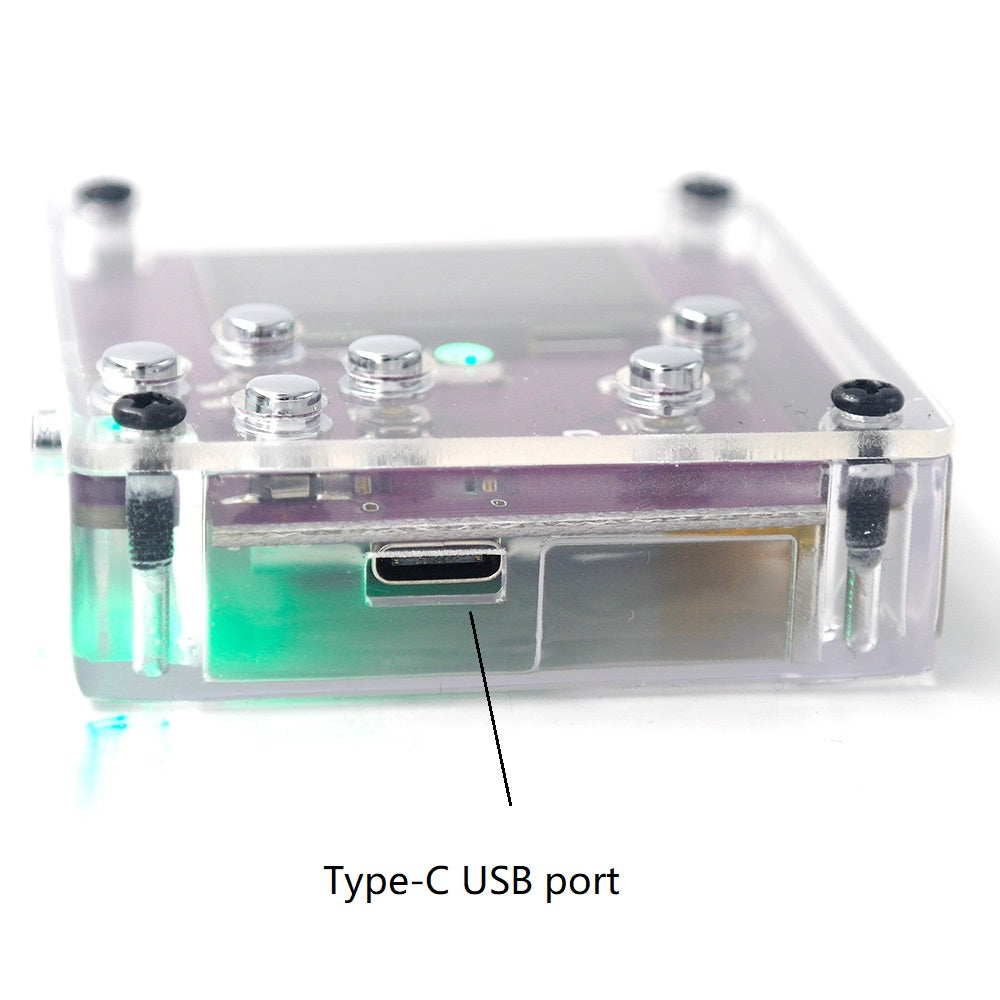
- Type-C USB support
Disclaimer
This project is a proof of concept for testing and educational purposes. Neither the ESP8266, nor its SDK was meant or built for such purposes. Bugs can occur!
Use it only against your own networks and devices! Please check the legal regulations in your country before using it. We don't take any responsibility for what you do with this program
Hardware info
- Display: SH1106 1.3" OLED
- Display SDA: GPIO 4
- Display SCL/SCK: GPIO 5
- WS2812b LED: GPIO 15
- Button Up: GPIO 14
- Button Down: GPIO 12
- Button LEFT: GPIO 16
- Button RIGHT: GPIO 13
- Button A: GPIO 2
- Button B: GPIO 0
More Info
Deauth
Closes the connection of WiFi devices by sending deauthentication frames to access points and client devices you selected. This is only possible because a lot of devices don't use the 802.11w-2009 standard that offers a protection against this attack. Please only select one target! When you select multiple targets that run on different channels and start the attack, it will quickly switch between those channels and you have no chance to reconnect to the access point that hosts this web interface.
Beacon
Beacon packets are used to advertise access points. By continuously sending beacon packets out, it will look like you created new WiFi networks. You can specify the network names under SSIDs.
Probe
Probe requests are sent by client devices to ask if a known network is nearby. Use this attack to confuse WiFi trackers by asking for networks that you specified in the SSID list. It's unlikely you will see any impact by this attack with your home network.